Managing Network Adapters with PowerShell: Addressing and Configuration Info
- Blog
- PowerShell
- Post
In my previous article, we started exploring working with network adapters in Windows Server 2012 using PowerShell. In that article, we looked at getting information from the physical adapter. Today let’s get some addressing and configuration information. As before, I’m running PowerShell 3 in a Windows 8 desktop that has RSAT (Remote Server Administration Tools) installed in a domain setting. The commands can be used remotely, but the server must be running Windows Server 2012 or later. Finally, in part three of this series I’ll explore PowerShell cmdlets that might come in handy when troubleshooting a networking issue.
Managing Network Adapters: Get-NetIPInterface
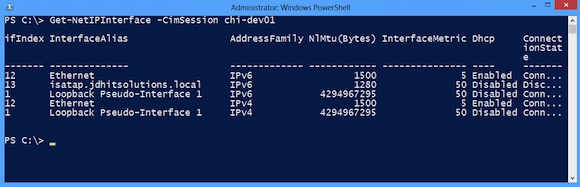
First, I want to track down interface information for a remote server
PS C:\> Get-NetIPInterface -CimSession chi-dev01
Results are displayed below in Figure 1.
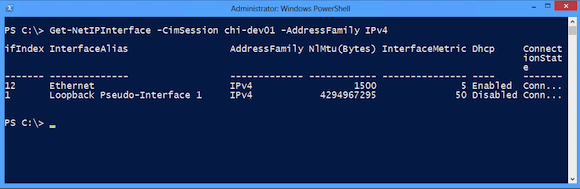
Since I’m not using IPv6 in my network, let me focus only on IPv4.
PS C:\> Get-NetIPInterface -CimSession chi-dev01 -AddressFamily IPv4
Figure 2 displays an easier-to-read result.
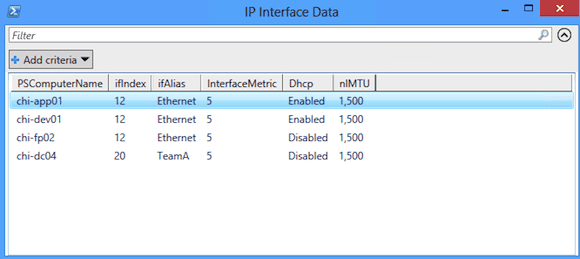
If I can do this for one, I can do it for many. Since I’m going to be querying remote machines more than once, I’ll go ahead and create some CIMSessions that I can reuse.
PS C:\> $cim = New-CimSession -ComputerName chi-dc04,chi-fp02,chi-dev01,chi-app01
Now I’ll repeat my previous command for all the computers and filter out the loopback adapters. But I’ll also need to tweak it to show the computer name.
PS C:\> Get-NetIPInterface -CimSession $cim -AddressFamily IPv4 -InterfaceAlias ethernet,team* | Select PSComputername,if*,InterfaceMetric,DHCP,nlMTU | Out-Gridview –title "IP Interface Data"
This will give me a nice list displayed in a sortable and filterable grid.
The interface index can come in handy when using the next cmdlets if a server has multiple adapters and you want to limit your query. I don’t have the situation in my test domain.
Getting More Info with Get-NetIPAddress
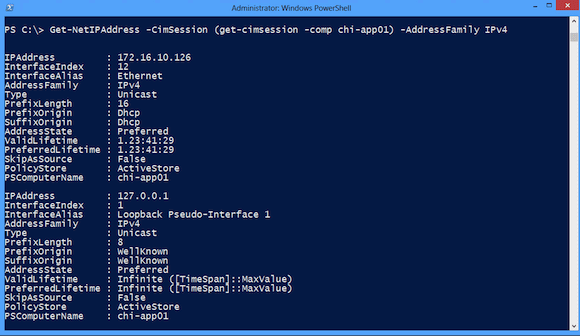
Based on the preceding, I can get an idea of the TCPIP configuration for each adapter. But I want more information, so I’ll turn to Get-NetIPAddress, focusing on IPv4 addresses.
PS C:\> Get-NetIPAddress -CimSession (get-cimsession -comp chi-app01) -AddressFamily IPv4
I want to re-use an existing CIMSession I’ve already created for CHI-APP01. You can see my results below in Figure 4.
I don’t really need to know about the loopback adapter, so I’ll filter it out. As before, I grab IPv4 address configuration for multiple servers.
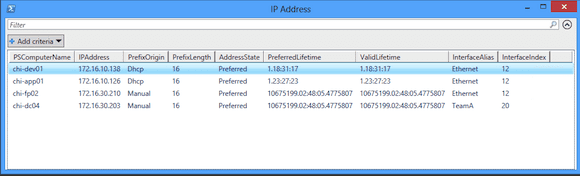
PS C:\> Get-NetIPAddress -CimSession $cim -AddressFamily IPv4 -InterfaceAlias ethernet,team* | Select PSComputername,IPAddress,Prefix*,AddressState,*Lifetime,Interface* | out-gridview -title "IP Address"
I know this seems like a lot to type – and if you need to do this on a regular basis, you’ll definitely want to turn this command into a script or function. Figure 5 illustrates the result.
Many of the cmdlets I’m demonstrating are designed to work together. I could also have used my earlier command getting IP Interface objects and pipe them to Get-NetIPAddress.
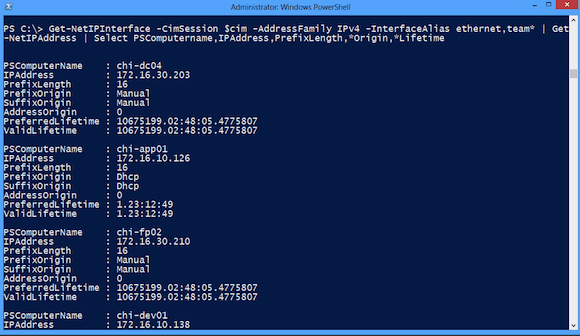
PS C:\> Get-NetIPInterface -CimSession $cim -AddressFamily IPv4 -InterfaceAlias ethernet,team* | Get-NetIPAddress | Select PSComputername,IPAddress,PrefixLength,*Origin,*Lifetime
This is sort of like running IPConfig remotely – plus, we get objects.
More Details with Get-NetIPConfiguration
Actually, we can more details on IP Configuration using Get-NetIPConfiguration. I think of this cmdlet as the IPCONFIG PowerShell equivalent.
PS C:\> get-netipconfiguration InterfaceAlias : Ethernet 3 InterfaceIndex : 17 InterfaceDescription : Microsoft Hyper-V Network Adapter #3 NetProfile.Name : GLOBOMANTICS.local IPv4Address : 172.16.30.8 IPv4DefaultGateway : 172.16.10.254 DNSServer : 172.16.30.203 172.16.30.200 172.16.10.1
Although the major benefit to the cmdlet is that it can query a remote computer.
PS C:\> get-netipconfiguration -CimSession (get-cimsession -comp chi-app01) InterfaceAlias : Ethernet InterfaceIndex : 12 InterfaceDescription : Microsoft Hyper-V Network Adapter NetProfile.Name : GLOBOMANTICS.local IPv4Address : 172.16.10.126 IPv6DefaultGateway : IPv4DefaultGateway : 172.16.10.254 DNSServer : 172.16.30.203 172.16.30.200
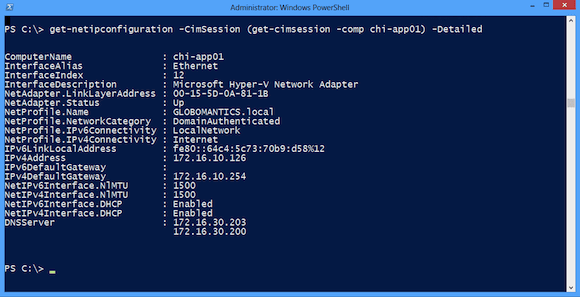
Or you can get detailed configuration information.
PS C:\> get-netipconfiguration -CimSession (get-cimsession -comp chi-app01) –Detailed
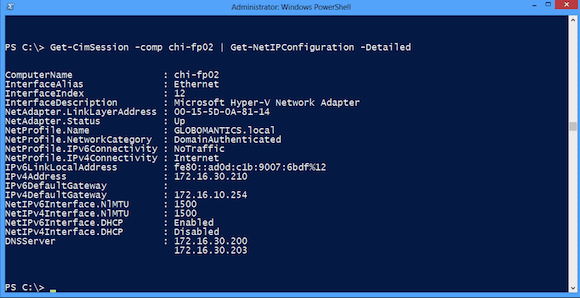
Querying remote computers is a little different, as the –CimSession parameter for Get-NetIPConfiguration won’t accept an array of sessions. However, you can pipe a CIMSession to the cmdlet.
PS C:\> Get-CimSession -comp chi-fp02 | Get-NetIPConfiguration –Detailed
Where it gets difficult is selecting the properties to display in gridview, export to a CSV, or build an HTML report. This is because many of the properties are themselves nested CIMInstances. The shell automatically unrolls everything when displaying to the console as I’ve done above. But anything else takes a little more work.
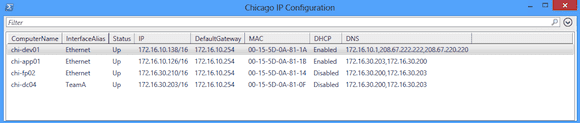
$cim | get-netipconfiguration -Detailed |
Select Computername,InterfaceAlias,
@{N="Status";E={$_.NetAdapter.Status}},
@{N="IP";E={"$($_.IPv4Address.IPv4Address)/$($_.IPv4Address.PrefixLength)"}},
@{N="DefaultGateway";E={$_.IPv4DefaultGateway.nexthop}},
@{N="MAC";E={$_.NetAdapter.MACAddress}},
@{N="DHCP";E={$_.NetIPv4Interface.DHCP}},
@{N="DNS";E={
($_.DNSServer | where {$_.AddressFamily -eq 2} |
select -ExpandProperty ServerAddresses) -join ","}}
This is definitely something you would want to script. But now I can run my CIMSessions through this and then to Out-Gridview, as you can see in Figure 9.
Based on this, I can see I need to make some configuration changes to a few servers. We’ll look at that in a future article.
As with everything I show you in PowerShell, be sure to read the full help and examples because I am not demonstrating every parameter and use case. I know it looks like a lot of typing, but most of the time that was because I wanted some specific information. If you are happy with the default console output, it doesn’t take much work to get network adapter information from Windows Server 2012 with PowerShell.
Next time we’ll look at some other information we can gather remotely.