In this five-part series I’ve been exploring Windows 8 Client Hyper-V. In the first article, I showed you how to install and configure the client Hyper-V feature in Windows 8. In part two, we configured a virtual switch, and in part three, I demonstrated how to populate Hyper-V with virtual machines. Part four saw us creating a new virtual machine from an existing VHD that had a previously installed operating system. I have a collection of VHD files that have been converted from my previously installed VirtualBox setup which I ran previously under Windows 7. I wanted to understand the process so I can re-build my test network under Hyper-V.
And finally, today in part five, we’re going to run through the steps in managing Windows 8 Client Hyper-V with PowerShell.
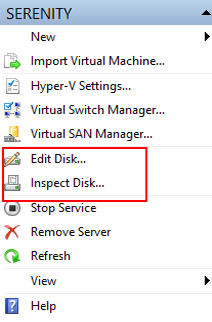
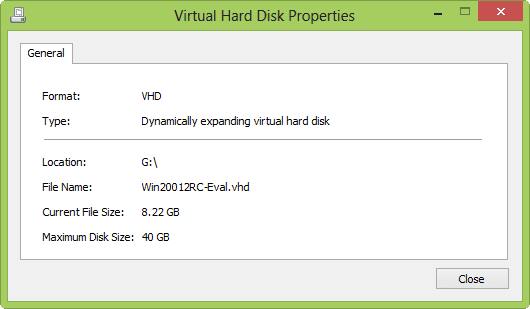
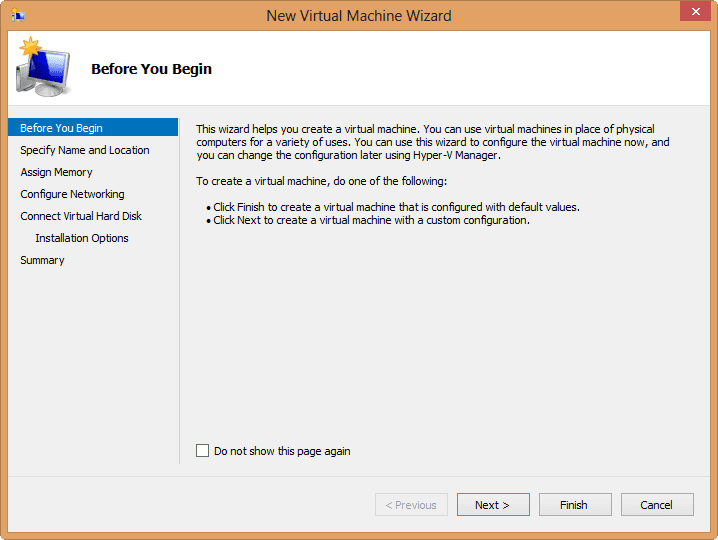
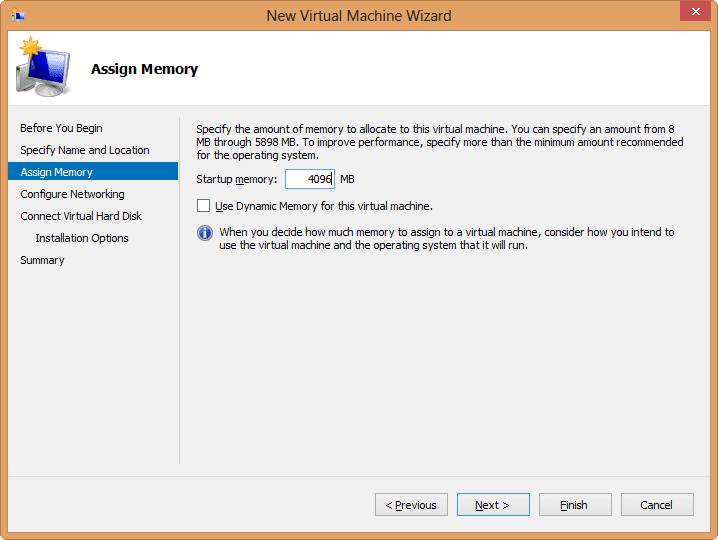
Now, if I wanted I could create a totally new virtual machine, and when wizard asks about the disk, I can create a new one as I show below in Figure 1.
I’ve set the size to 20GB and am using the default location. Hyper-V will also help me get an operating system installed on the new disk.
I can install an OS from the CD/DVD drive in the host machine or even from an ISO. If I choose to install an OS later, it is up to me to make the necessary virtual machine configurations to mount the installation media. But since I don’t have existing test machine for Windows 8, I’ll go ahead mount the ISO, as I show below in Figure 3.
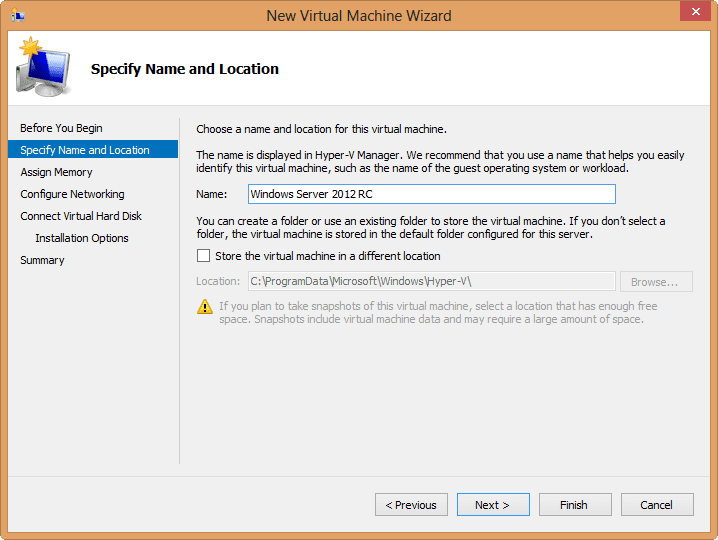
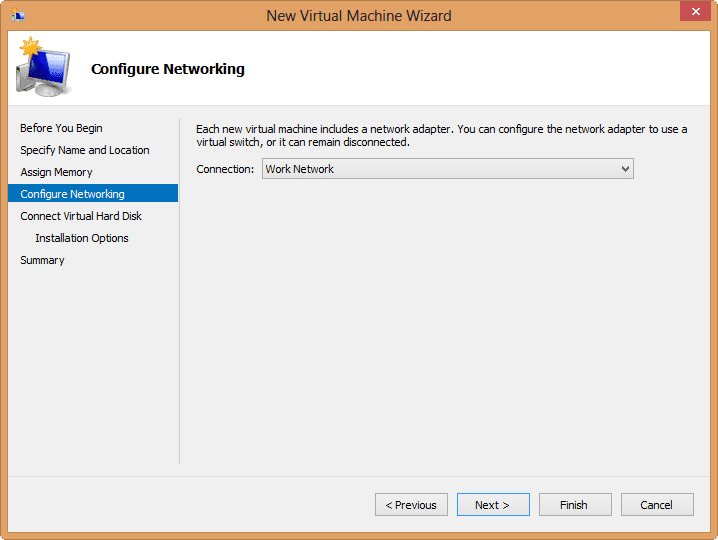
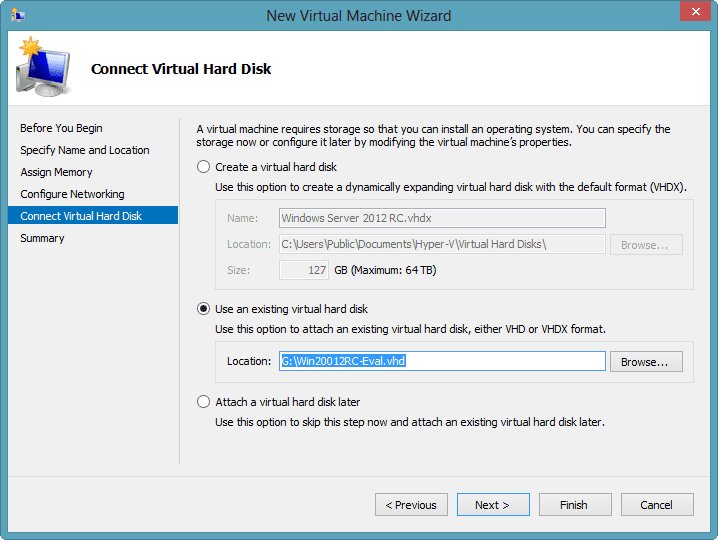
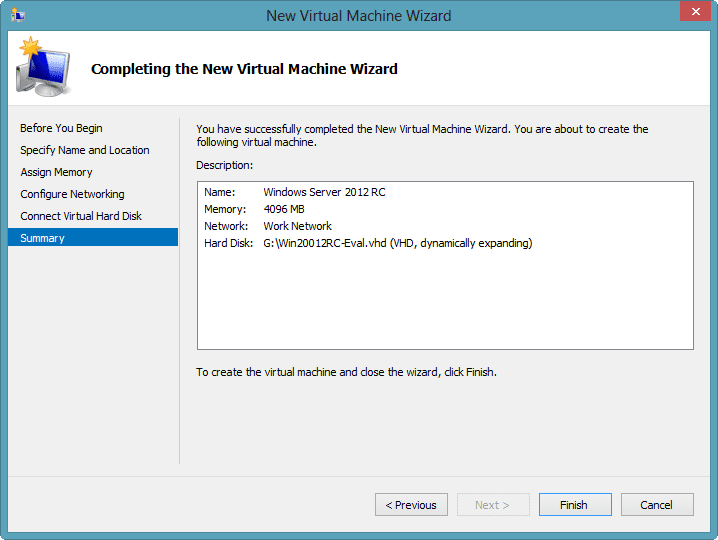
After I finish the wizard, then I can fire up the virtual machine and it should go through the install process. But I already have a folder of VHD files I want to use. I’m going to create a new virtual machine using the wizard for one of the VHDs. Figure 4 depicts the end result.
My virtual machine is running Windows Server 2008 R2 Core with a static IP on a single adapter. I boot up the machine, make sure everything works including integration services and am ready to go! As much as I liked VirtualBox, having everything in Hyper-V makes my life easier and opens up new management opportunities (some of which I’ll cover in future articles).
However, I don’t want to manually click through the wizard to create a dozen or so virtual machines from my saved VHD files. So I’ll turn to PowerShell, which is one of the reasons I’m excited about moving to Hyper-V on Windows 8. When I enabled the Hyper-V feature in Part 1, I also made sure to include the PowerShell module. This module has all the tools I need to manage Hyper-V from PowerShell, including creating new virtual machines.
PS C:\> get-command -module Hyper-v
You can see the results in Figure 5.
The cmdlet I’m going to use is New-VM. Cmdlet help is shown below in Figure 6, but you will want to look at full help on your computer.
Thus to create a new virtual machine from the PowerShell prompt I can use a command like this:
PS C:\> New-VM -Name "XP Lab" -VHDPath D:\VHD\XPLab.vhd -MemoryStartupBytes 512MB -BootDevice IDE -SwitchName "Work Network" -whatif What if: New-VM will create a new virtual machine "XP Lab".
I love the –WhatIf parameter so I can verify I haven’t made an error. The memory parameter defaults to 512MB, but I wanted you to see how to set that. The VHDPath parameter is the path to my existing VHD file. The virtual machine itself will be created in the default location. Or I could have used –Path to specify a different location. I’ll rerun the previous command without –Whatif and I have success.
The virtual machine has many properties that I can manage from PowerShell. But for now all I want to do is to take a quick baseline snapshot. I can do this with the Checkpoint-VM cmdlet.
PS C:\> Checkpoint-VM -Name "XP Lab" -SnapshotName "Baseline" -Passthru VMName Name SnapshotType CreationTime ParentSnapshotName ------ ---- ------------ ------------ ------------------ XP Lab Baseline Standard 8/20/2012 6:00:13 PM
At this point I’m ready to fire up the new VM for the first time.
Now that I know how to do this, I can do it for many. I created a simple CSV file for the virtual machines I want to recreate.
Name,VHD,Memory "CHI-DC02",D:\VHD\CHI-DC02.vhd,1073741824 "CHI-FP01",D:\VHD\Globomantics-01.vhd,1073741824 "CHI-DC01",D:\VHD\Globomantics-DC.vhd,1073741824 "CHI-Client01",D:\VHD\Win7-2.vhd,2147483648 "CHI-Client02",D:\VHD\Win7_C.vhd,2147483648
I can then import the CSV file in PowerShell and pipe the results to ForEach-Object. In the loop I’ll create a new virtual machine based on the imported data. Because the New-VM writes a virtual machine object to the pipeline, I can go ahead and pipe directly to Checkpoint-VM to create my baseline snapshots. Here’s the code I’ll run:
import-csv D:\importvm.csv | foreach {
Write-Host "Creating $($_.Name) from $($_.VHD)" -ForegroundColor Green
New-VM -Name $_.Name -VHDPath $_.VHD -MemoryStartupBytes $_.Memory -BootDevice IDE -SwitchName "Work Network" | Checkpoint-VM -SnapshotName Baseline
}
You can see the results below in Figure 8.
Hyper-V Manager also shows my “new” virtual machines. Now I can fire them up, do a little cleaning up, and I’m ready to go.
Mind you, I had nothing against VirtualBox — it was free and fit my needs. But now with Windows 8 I have a rock-solid desktop virtualization product that is easy to set up and manage. Plus I have the added bonus of managing my new Hyper-V environment directly from PowerShell.