Linux for Windows Server Administrators: File System Rights
In this third installment of our Linux for Windows Server administrators article series, we’ll take a look at Linux file system rights, which you’ll likely need to dive into at some point. In this article, you’ll learn all you need to know for managing user rights on a Linux server.
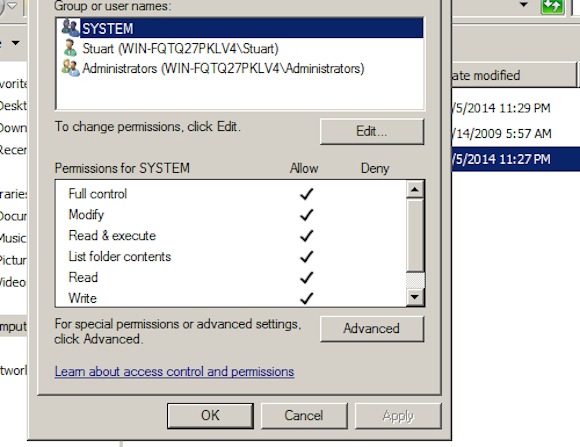
Although Linux’s file system rights work in a similar fashion as Windows, there’s a few differences and gotchas. One big difference is that in Windows a user does not have their own group, but a default shared group of “Users” in Windows, assuming we’re on a standalone Windows system.
An Introduction to Linux File System Rights
Let’s start by taking a look at my home directory. It shows a basic file that I created for this example, testfile.txt. To get the same screen, you’ll need to use “ls -l” on the command line to obtain detailed listing of directory contents as shown below.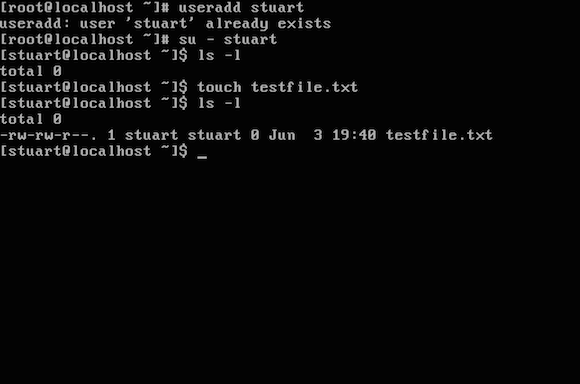
Understanding Linux User ID (UID) and Group ID (GID)
When a user account is created, it is given a User ID (UID) and a Group ID (GID). UID uniquely identifies the user, while the GID that identifies the group should also be unique. This provides us with the tools needed to grant rights to the UIDs and GUIDs. Each security attribute has a weight or value associated with it. Behind the scenes the weighting goes as follows: Read is 4, Write 2, Execute 1 or — which has a weighting of zero and effectively means no rights. One thing to note is that if a user does not have execute rights, then they cannot enter the directory. This is where you might see people who are new to Linux being lazy and using the mindset of “just get it to work” by giving Linux files the rights mask of 777 (Read, Write and Execute). This lets anyone read, write and execute the file. Needless to say, using 777 is not a good idea in most circumstances, especially on external facing systems. Changing the rights is quite straightforward, thankfully. If we have a group and we only want them to be able to read and download the file but the owner needs to be able to update it, we can use the following command: chmod 664 myfile.txtThis gives the user read and execute (Remember: Read is 4, Write is 2) permissions and everyone else just read permissions. This can be modified to give different access to different users. It is also possible to setup default rights on newly created files, both locally on a per user and a group basis. This is done with what is known as a umask. This is usually set to 002 and is in effect subtracted from the initial rights that a file has. It provides a way to control the rights on newly created files. You can set the umask quite easily by issuing the command umask 002. You would use this command to prevent files from being made executable by default, as an example. Each column maps to the User, Group and Other.
Linux Primary and Secondary Groups
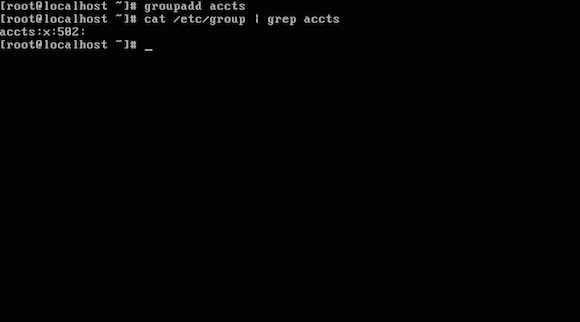
In Linux, there are two types of groups, primary and secondary. Rarely will you want to modify the primary group. When you create a file, by default, the file created has your UID as the default group. The following is a simple command that shows which groups a user belongs to: groups stuartFor a more involved example, let’s say we want to run a fictitious accounts department. We want our group of accountants to be able to edit and update the files, and the files to be owned by the group rather than individuals. The following steps describe how to do this: 1. Create a new group and give it a name. I am creating a shared folder in the root directory, imaginatively called “shared” using the command mkdir /shared (Note: I realise that in a production environment the server should not be on, and I recommend giving it its own partition.) 2. Next, add a new group. To add the group, use the command as shown below:
groupadd testersA user can be a member of several groups. An example would be “id stuart” as it’s shown in the graphic below. 3. Next, it’s a good idea to remove the “Other” rights from /shared. As you know from previous installments in this articles series, the command we need is chmod, so type:
chmod 770 /sharedNotice in the screenshot that we have an entry in the etc/group file.
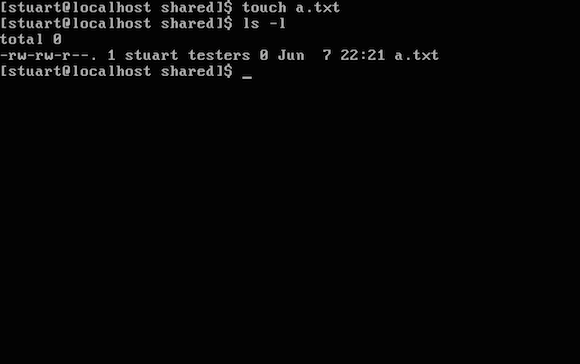
usermod -a -G testers stuart5. You can add several users in one command, chaining one user after the next. If we let a user create files that would mean that the file owner would be the individual owner in both the UID and GID. Fixing that problem is quite straightforward. Again, we fall back to using the chmod command:
chmod g+s /sharedThis is known as an Set Group ID (SGID). This lets us create files in the folder, and the file inherits the group rights. Lastly, the following command prevents deletion of files by anyone except the owner.
chmod o+t /shared
chmod g+o myfileYou can can vary the use of it to use o for owner, g for group and o for other. Then you can add or remove the rights using a + or a – symbol. Lastly add the rights (r, w or x if you had forgotten) and the filename. In summary, this is a basic introduction to managing files and users in Linux. There are additional things that you can do to make the control more fine grained, but are beyond the scope of this basic file system intro. I would also suggest that you take your time and make sure you get the rights correct as frequently virtual break-ins are related to lax file rights. If you’d like to review the Linux articles we’ve posted so far, I’ve included links to them below.


