How to Configure Group Policy to Reapply Settings
Active Directory Group Policy is a configuration management tool used by organizations to apply settings to servers and workstations. But the way Windows processes Group Policy Objects (GPOs) isn’t straightforward. I’m not going to give a complete rundown of how Group Policy processing works in this article but talk about one specific aspect.
Group Policy Processing
Windows processes GPOs that apply to a device during computer start up and shutdown; and when users log in and log off. These events are known as foreground processing. Additionally, by default Windows processes Group Policy every 90 minutes for workstations and every 5 minutes for servers when users are logged in. This is known as background processing. But regardless of whether foreground or background processing is used, the default behavior is to only reapply a GPO’s settings if the policy object was modified before the refresh. In principle, a user could modify a registry setting that is managed by Group Policy and it would never be reverted to the value defined in the GPO. This default behavior is designed to speed up Group Policy processing.
Force Group Policy to Reapply Settings
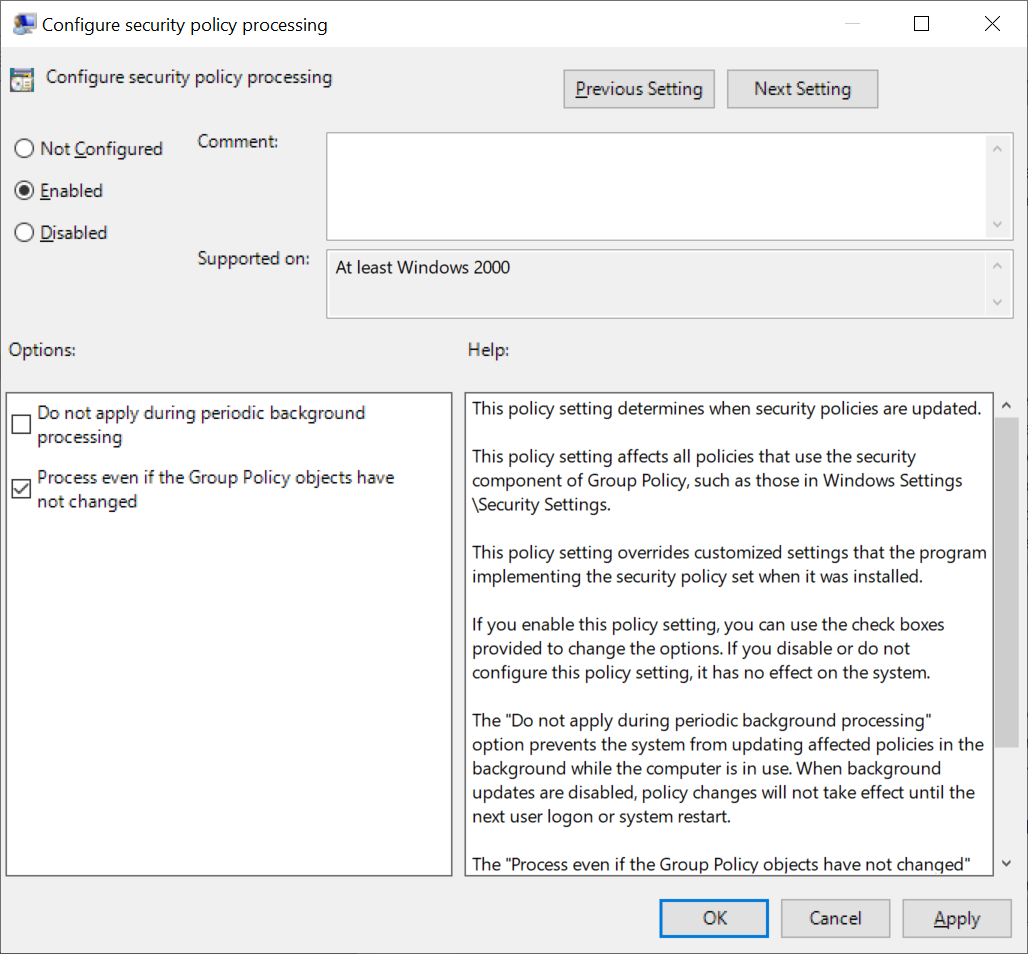
If you want to make sure that security settings in a GPO are applied every time Group Policy is processed, regardless of whether the GPO has changed, there are four Group Policy settings that you should enable. You can find them under Computer Configuration > Administrative Templates > System > Group Policy.
- Configure security policy processing
- Configure registry policy processing
- Configure scripts policy processing
- Configure IP security policy processing
Set each policy to Enabled and check Process even if the Group Policy objects have not changed. Remember that enabling these settings may impact logon performance.
You can also force settings be reapplied for several other categories:
- Configure folder redirection policy processing
- Configure Internet Explorer Maintenance policy processing
- Configure wired policy processing
- Configure wireless policy processing
If you are new to Group Policy, check out How to Create and Link a Group Policy Object in Active Directory and Using GPUpdate to Manage Group Policy on Petri. You can use the instructions in the article to help you create and edit Group Policy Objects using the Group Policy Management Console (GPMC), which is part of the Remote Server Administration Tools (RSAT) for Windows 10 and accessible from Server Manager in Windows Server. In Windows 10 version 1809, RSAT is a Feature-On-Demand that can be installed in the Apps section of the Settings app by clicking Manage optional features. In earlier versions of Windows, you’ll need to manually download the correct version of RSAT and install it from Microsoft’s website.
You can manually trigger background Group Policy processing using the gpupdate command-line utility. If you want all GPO settings to be applied, regardless of whether GPOs have changed, add the force switch as shown here:
gpupdate /force
Most security settings that are managed by Group Policy can only be modified by users that have administrative rights. You could argue, that if a user already has administrative privileges, it is already potentially game over. But nevertheless, if you want to increase the likelihood that devices are configured to a known standard, then you might want to think about enabling these settings. Microsoft gives you quite a lot of flexibility in which settings are ‘always processed’, allowing you to strike a balance between security and performance that suits your organization’s needs.
Related Article: