How to Block Unwanted Apps in Edge and Windows 10
Windows 10 protects users from malicious downloads using a feature called SmartScreen. Windows Defender SmartScreen uses reputation-based protection to defend users against phishing and malware websites and applications, and potentially malicious files.
SmartScreen has two mechanisms for protecting users. First, it analyzes webpages for suspicious behavior. Secondly, sites and apps are checked against a constantly updated list of reported malicious sites. If a webpage is deemed suspect or it is on Microsoft’s list, SmartScreen displays a warning that the page may not be safe.
Potentially Unwanted Apps
Potentially Unwanted Apps (PUA) are not viruses or malware. Microsoft defines PUAs as other types of threats that might affect Windows performance or use; or that have a poor reputation. Examples of PUAs include software that contains advertising, app installers that bundle offers to install other software that isn’t signed by the same certificate as the downloaded file, and apps that are designed to evade security software.
Windows 10 May 2020 Update Potentially Unwanted App protection
Users that are running the Windows 10 May 2020 Update or later can enable PUA protection in the Windows Security app.
- In the search box in the bottom left corner of the taskbar, type security.
- In the list of search results, click Windows Security.
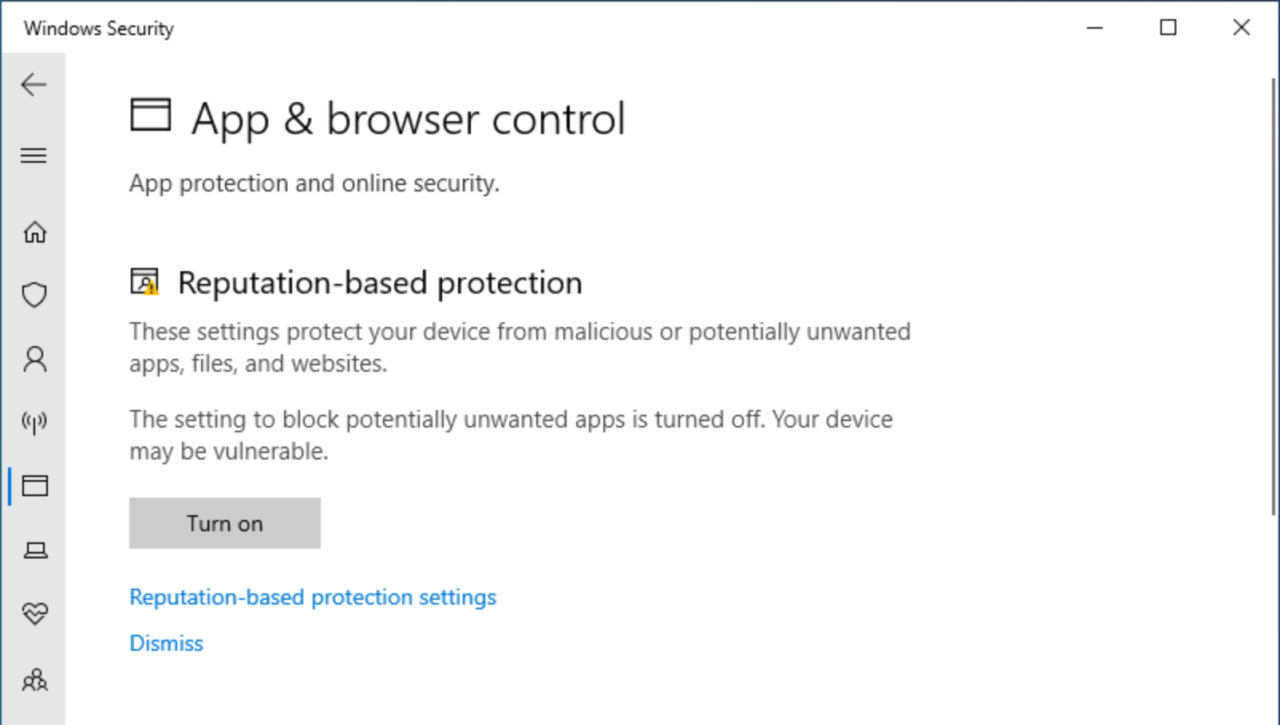
- Click App & browser control on the right of Windows Security.
- On the App & browser control page, click Turn on under Reputation-based protection. You may be required to confirm the operation in a User Account Control security prompt.
- Now click Reputation-based protection settings.
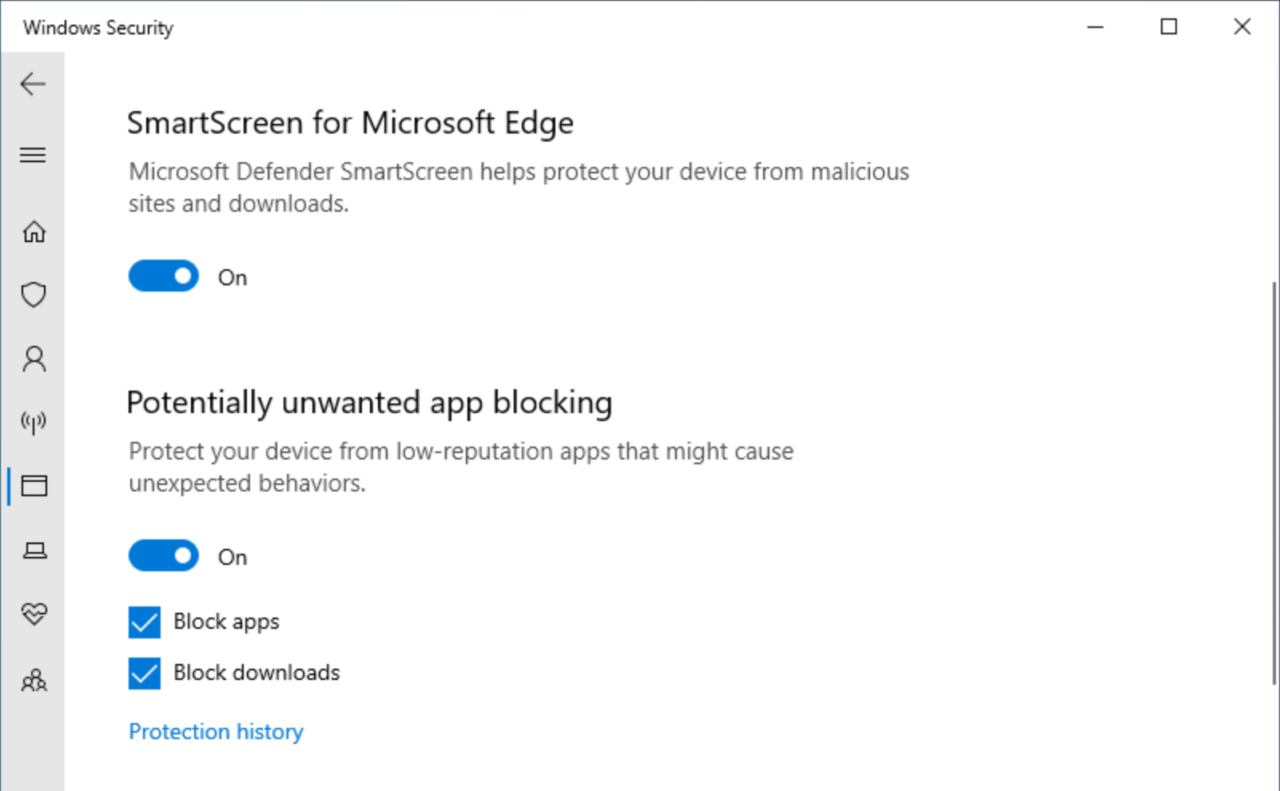
- Scroll down to Potentially unwanted app blocking and check that the toggle switch is set to On.
- Make sure that Block apps and Block downloads are both checked.
- Close Windows Security.
If you are using the new Edge browser, enabling PUA Block downloads in Windows Security turns on PUA protection in the browser settings, which you can find here: edge://settings/privacy
Potentially Unwanted App protection in earlier versions of Windows 10
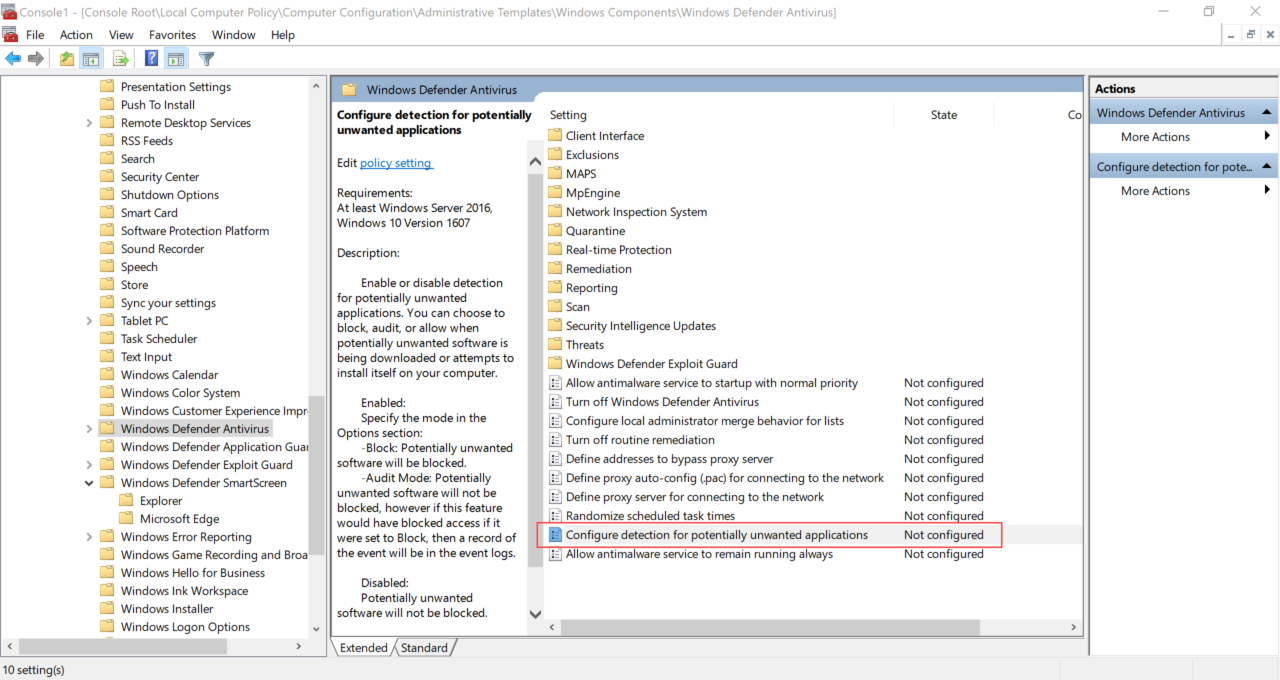
If you are using an earlier version of Windows 10, PUA protection can be enabled using Group Policy. All you need to do is enable the Configure detection for potentially unwanted applications setting under Computer Configuration > Administrative Templates > Windows Components > Windows Defender Antivirus.
Once Configure detection for potentially unwanted applications is set to Enabled, choose Block or Audit mode from the menu under Options. Selecting Block displays a warning message to users if a malicious app is detected. Audit mode records an event in the event log without displaying a warning message to users.
For more information on using Group Policy, see How to Create and Link a Group Policy Object in Active Directory on Petri.
Potentially Unwanted App protection in Microsoft Edge
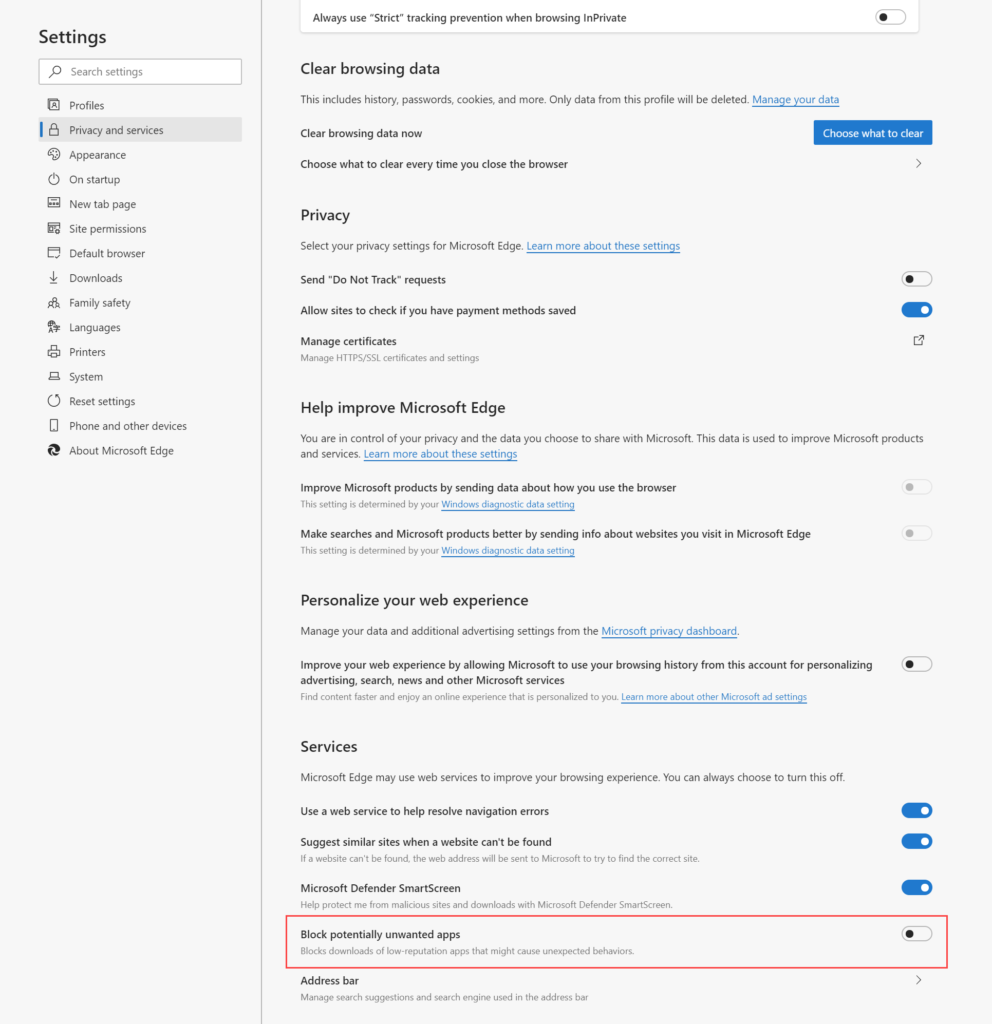
As I mentioned above, the new Microsoft Edge browser also has a setting where you can enable PUA protection.
- Paste the following URL into the address bar: edge://settings/privacy
- Scroll down to Services and then toggle Block potentially unwanted apps to On.
- Close the Settings tab.
Testing SmartScreen protections
PUA protection isn’t enabled by default in the Windows 10 May 2020 Update. If you haven’t already tested the feature, run a pilot in your organization to determine whether it is effective and that it doesn’t block files that users need to download. You can test out PUA protection and other SmartScreen protections at the SmartScreen demo pages here.