Friday Funny: The Computer Man
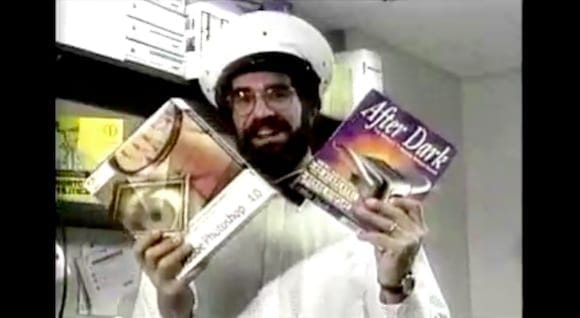
Remember when Windows 95 was the latest and greatest OS from Microsoft, and the Macintosh — and Apple — were years away from the popularity they enjoy today? Here’s a painfully awkward video from 1995, where a self-styled “Computer Man” hands out boxed copies of software to dancing office workers and extols the virtues of the Macintosh over the “plug and pray” nature of Windows 95, all while singing an IT-focused ditty based on the “Scatman” song by Scatman John. (Video below image)
He’s the “Macintosh Man with virus scan.”
It wasn’t long after this video was made that Apple and the Macintosh had a near-death experience and began licensing out the Mac OS to third-party hardware manufacturers. Steve jobs returned to Apple in 1996, and the rest is history: Apple is currently the most valuable technology company in the world based on market capitalization, and may likely remain in that position for the foreseeable future.