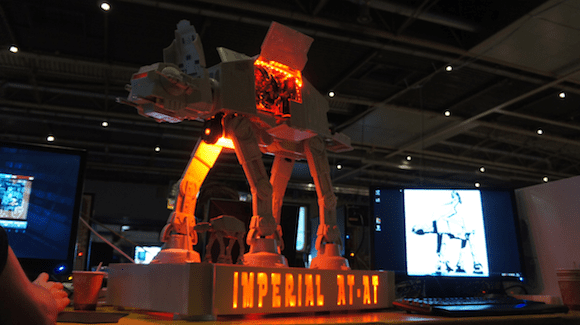
The Friday Funny: Star Wars AT-AT PC Case
Building your own PC can be a rewarding experience, and thousands of tech-savvy PC fans do that every year. As is the case with all custom creations, the more creative among us can sometimes create genuine works of art that stand apart from the mundane. Such is the case — if you’ll pardon the pun– with this creation from case designer Asphiax, who has created a PC case in the form of the Imperial AT-AT walker from the Star Wars films.
The Imperial Walker At-AT PC case (case and photo by Asphiax)
So have you built your own custom PC case? Drop me an email with your best designs, and we’ll feature entries we receive in a future blog post.
- Follow Jeff James on Twitter (@jeffjames3) and Google+ (add Jeff to your circles)
- Follow Petri IT Knowledgebase on Twitter (@petri_co_il)
- Follow us on Facebook and Google+ as well!