Enable Advanced Auditing in Windows Server
How do I enable Advanced Audit Policy Configuration in Windows Server?
With the ever-increasing need to meet industry or governmental compliance mandates, the ability to properly audit and report on what is happening in our environments is crucial. In Windows Vista, Microsoft divided the original nine auditing categories into subcategories and added some new events that weren’t previously possible to audit, such as the ability to track access to remote storage devices, which increased the total number of events that can be audited to 53.
Starting in Windows Server 2008 R2 and Windows 7, Advanced Audit Policy Configuration in Group Policy allows administrators to configure the new granular audit settings without the need to use auditpol.exe at the command line.
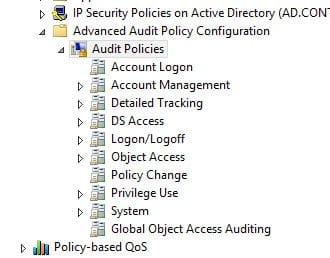
Advanced auditing allows for more granular audit configuration, so that only events you are interested in capturing are written to the Event Log. The new settings can be found in Group Policy under Computer Configuration\Policies\Security Settings\Advanced Audit Policy Configuration, and the original audit settings can be found here: Security Settings\Local Policies\Audit Policy.
You’ll see that in the basic audit settings, it’s possible to switch account logon auditing on or off, but in the new advanced configuration there are four different account logon events that can be audited:
- Audit Credential Validation
- Audit Kerberos Authentication Service
- Audit Kerberos Service Ticket Operations
- Audit Other Account Logon Events
Enabling Advanced Audit Policy Configuration
Basic and advanced audit policy configurations should not be mixed. As such, it’s best practice to enable Audit: Force audit policy subcategory settings (Windows Vista or later) to override audit policy category settings in Group Policy to make sure that basic auditing is disabled. The setting can be found under Computer Configuration\Policies\Security Settings\Local Policies\Security Options, and sets the SCENoApplyLegacyAuditPolicy registry key to prevent basic auditing being applied using Group Policy and the Local Security Policy MMC snap-in.
Configuring Advanced Audit Policy settings
Now that you’ve disabled basic auditing, you can navigate to the Advanced Audit Policy Configuration node and enable auditing for any of the subcategories. Bear in mind that Group Policy can’t be used to enable advanced auditing on Windows Vista or Server 2008, but instead you can use the auditpol.exe command line tool in a logon script.
To see which audit policies are enabled, run auditpol.exe /get /Category:* at the command line. This will list all the subcategories and show their status. In this example I’m going to set success and failure auditing for the Sensitive Privilege Use subcategory: auditpol.exe /set /subcategory:”Sensitive Privilege Use” /failure:enable /success:enable