EIGRP Metrics Troubleshooting
- Blog
- Networking
- Post
Overview
When implementing any routing protocol, it is vital to have a handle on how the protocol operates and makes decisions. Without this knowledge, it is almost impossible to check and make sure that the protocol is configured properly and is operating as expected. This article takes a look at the Enhanced Interior Gateway Routing Protocol (EIGRP), how its metric is calculated, and how this information can be used to ensure that traffic is taking the path that is expected.
EIGRP Metric Calculation
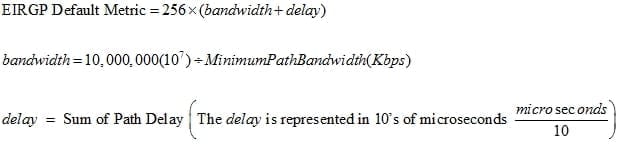
Unlike OSPF, the EIGRP metric can be complex to calculate and is calculated differently depending on the configuration of the EIGRP device. By default, the EIGRP metric is calculated as shown in Figure 1:
Figure 1 – EIGRP Default Metric Calculation
As shown in Figure 1, by default, the EIGRP metric only takes into account the bandwidth and delay parameters of a network path to calculate the metric. It does have the ability to take into account a number of additional parameters, including load and reliability. These are reflected in the complete EIGRP metric, which is shown in Figure 2:
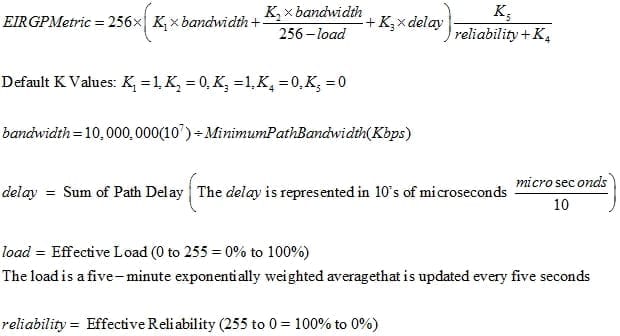
The k-values shown in Figure 2 can be used to alter the metric and give additional weight to certain network parameters. On most modern networks, the default k-values and default metric calculation are used.
Figure 3 displays a simple network topology that will be used to calculate a sample EIGRP metric.
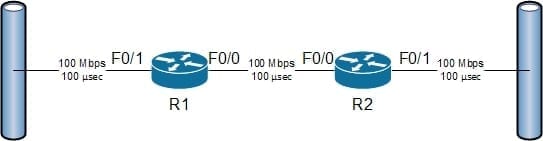
Assuming that EIGRP is configured, R1 would have an EIGRP routing table entry for the network that is connected to R2’s F0/1 interface. R1 would calculate the EIGRP metric for the path between it and the destination network; in this case, this would involve passing through its F0/0 interface and through R2’s F0/1 interface. The first part to figure out for the EIGRP metric is the minimum path bandwidth; as stated above, the path for R1 goes through its F0/0 interface and through R2’s F0/1 interface, which both have the same bandwidth of 100 Mbps. The bandwidth metric calculation is shown in Figure 4:
The next part includes adding up the total delay across the entire path to the destination. In this example, the delay on both links is 100 µsec for a total of 200 µsec of delay across the entire path. Keep in mind that when calculating the delay part of the EIGRP metric, that delay is not represented in µseconds but in 10’s of µseconds. The delay metric calculation is shown in Figure 5:
These two parameters are then inserted into the EIGRP formula and a metric is found; this is shown in Figure 6:
It is very important to note that the bandwidth that EIGRP is using in its metric calculations is based on the configured interface bandwidth using the bandwidth interface configuration mode command. The bandwidth that is configured with the bandwidth command does not have to match the physical bandwidth of the interface, and does not affect the physical bandwidth of the network.
It is also possible to alter the delay of an interface that is used by EIGRP for its metric calculation; to do this, the delay command is used. Like the bandwidth command, the delay command does not alter the actual delay of an interface, but simply the value that is used to calculate the metric.
As shown in Figure 2 above, there are a number of EIGRP k-values that can be changed to affect how the metric is calculated. Each of these k-values can be any value from 0 through 255; to alter these values use the metric weights command while in router configuration mode (router(config-router)#). It is typical to leave the default values, but network engineers should be familiar with the possibility of k-value changes. Look for this command in the configuration if the EIGRP metrics are not calculating correctly (based on the default metric formula).
Summary
Most of the time when routing protocols are implemented on small simple network topologies, they work without much additional configuration. When working on networks that are larger, the complexity of the routing protocol configuration can increase. This complexity and the size of the topology can make troubleshooting very complex as well. The EIGRP metric, unlike the OSPF metric, can be very complex to calculate and remember. It is important for any engineer that will work on an EIGRP network to be familiar with how the EIGRP metrics are calculated on their network (default or otherwise). Without this information, it is impossible to troubleshoot how the route to a destination is calculated.