How to Search for Deleted Objects in Active Directory
Overview
If you have ever wondered where you can find an object that was deleted from the Active Directory or if you ever wished to see the details of your lost objects, this article can help you.
Let’s say you were called in to assist a Systems Administrator that could swear he used to have a specific computer account but now it’s gone and you have to find it – with these instructions, you have the ability to do it!
Searching for Deleted Objects in Active Directory
Before we get started, just a quick reminder. When an object is deleted from Active Directory, it is not immediately erased, and instead it is marked for future deletion. The marker used to designate that an AD object is scheduled to be destroyed is called a “tombstone.” A tombstone is an object whose IsDeleted property has be set to True, and it indicates that the object has been deleted but not removed from the directory, much like a deleted file is removed from the file allocation table but the data is not actually removed from the drive. The directory service moves tombstone objects to the Deleted Objects container, where they remain until the garbage collection process removes the objects (this process is performed every 12 hours by default). The length of time tombstone objects remain in the directory service before being deleted is either 60 days for Windows 2000/2003 Active Directory, or 180 days for Windows Server 2003 SP1 Active Directory (by default).
Just pay attention to one important issue: if you want to review all the object’s attributes, you must have the Active Directory Recycle Bin enabled on the server (Windows Server 2008/R2 – we’ll discuss that in a different article).
Follow the steps below on one of your Domain Controllers where ldp.exe is available. Ldp.exe is built in to Windows Server 2008/R2, or is available as a separate download from Microsoft as part of the Support Tools in Windows Server 2003.
-
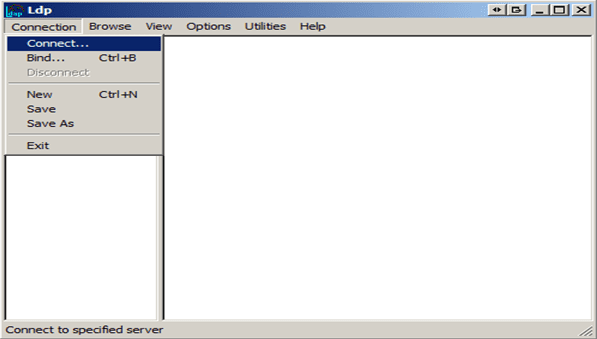
- Click Start -> Run, and then type ldp.exe
- Connect to a Domain Controller by using menu Connection -> Connect… and type the Domain Controller name.
-
- Authenticate to the Domain Controller by menu Connection -> Bind… and choose the right credential.
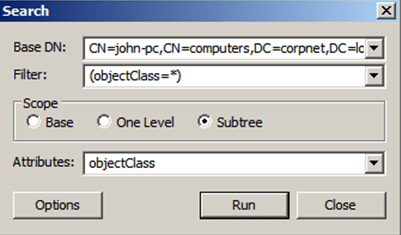
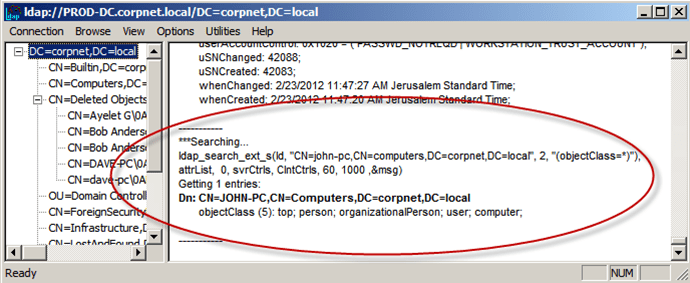
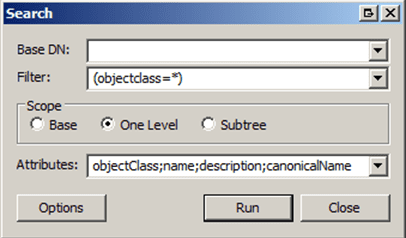
I have created a computer account called “john-pc” just to show you how it looks before the deletion; in this example the domain name is “corpnet.local.” - From the menu, choose Browse -> Search.
In the Base DN field, you can type either the path of the desired object, or the distinguished name of your domain, or both. In this case let’s use the above example and search for: “CN= john-pc,CN=computers,DC=corpnet,DC=local.”
- Authenticate to the Domain Controller by menu Connection -> Bind… and choose the right credential.
-
- Click on Run to start the search.
-
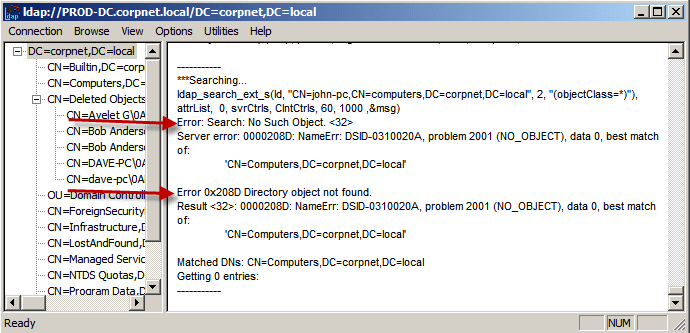
- Now let’s delete the object from Active Directory and search for it again.
- If we search the same way as before with the same parameters, we will get the error:
-
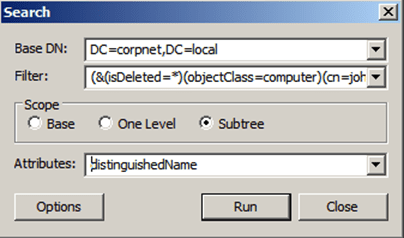
- From the menu, choose Browse -> Search
.
-
- In the Base DN field, type the distinguished name of the domain, or path of the object that you want to locate. Using our example, I will type “DC=corpnet,DC=local.”
- In the Filter field, you have to describe which object you are looking for, so we will use:
“(isDeleted=*)” for it has been deleted,
“(objectClass=computer)” because I am looking for a computer account that was deleted,
“(cn= john-pc*)” if I want to be more specific and look for this object only and not for all the computer accounts that have been deleted.
And to combine all the conditions together, type (without the quotes):
(&(isDeleted=*)(objectClass=computer)(cn= john-pc*))
-
- In the Scope area, select Subtree.
- In the Attributes field, we need to determine which attributes of the object we want to display, and as I said at the beginning, it depends weather “Active Directory Recycle Bin” is enabled on the server.
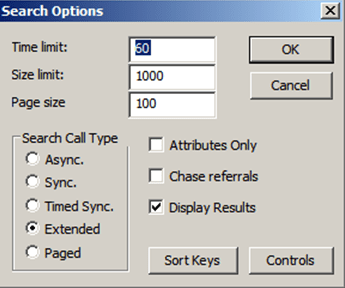
Asterisk (*) will show me as much details as possible. - Click on the Options button. The Search Options dialog box will appear:
-
- Verify that all the 3 fields: Time limit, Size limit and Page size, contains a value that is higher than 0 (zero).
- In the Search Call Type area, select Extended.
-
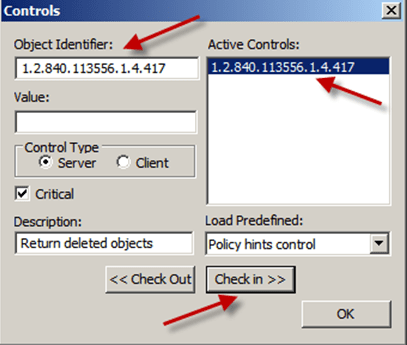
- Press on Controls and then type 1.2.840.113556.1.4.417 in the Object Identifier box.
-
- To add the control to the Active Controls list, click Check in.
- In the Control Type section, select Server, then click OK.
- In the Search Options dialog box, click OK.
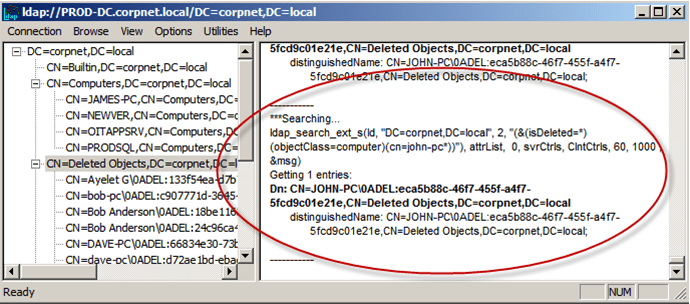
- In the Search dialog box, click Run and you will get the result:
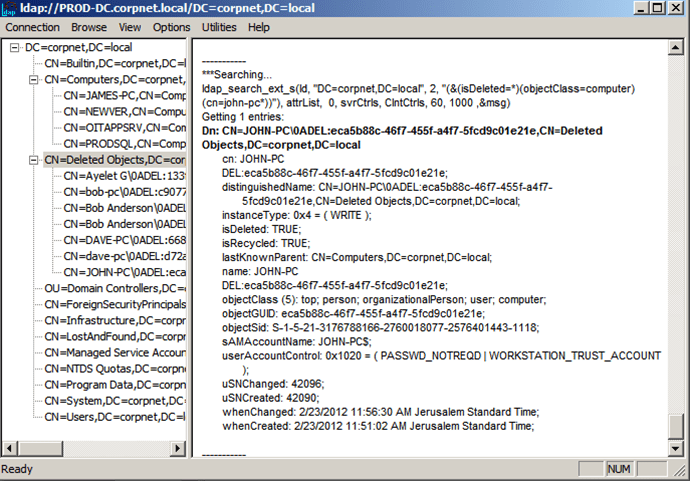
And just to clarify section 10, if I use * as the attribute instead of “distinguishedName”, the output will be:
Now, after you found the deleted object, you can reanimate it, which is a fancy word for restoring the deleted object. Remember that reanimating a deleted object doesn’t immediately restore it to its original properties. For that, you will need to either restore the object from a backup (performing what is called an authoritative restore), use AD Snapshots (a feature found in Windows Server 2008/R2), or use the AD Recycle Bin feature (part of Windows Server 2008 R2).
Conclusion
Those are the steps you need to take in order to find an object that was deleted from the Active Directory. Remember that when an object is deleted from Active Directory, it is not immediately erased, but instead marked for future deletion.