What Are Service Manager Configuration Items?
Configuration items in Service Manager refer to data that is stored in the database regarding items such as users, computers, services, virtual machines, templates, and so on. These items can then be used when submitting forms, such as those created as part of a private cloud infrastructure fulfillment request or as part of an incident, problem, or change request form. In today’s post, I’ll present a quick introduction to configuration items in Service Manager and show you how to create configuration items.
Configuration Item Types: Services
Another type of configuration item is a service, which differs slightly from a standard item in that it contains technical and business related data. A service is typically used to assess the business impact of an incident or to analyze what effect a change can have across shared infrastructure. A service can also hold key information about service owners, customers, and users. Services are often used to help you manage a work item.
Configuration items are often populated automatically by one of the Service Manager’s connectors – for example, key information about private cloud services and templates that you have deployed or have created are imported through the Operations Manager and Virtual Machine Manager connectors.
Creating Configuration Items
While our introduction to configuration items (CIs) thus far has been from the perspective of automated creation of these items, this is really to support scale and convenience. If you choose not to leverage the connector framework to establish the configuration items, that is perfectly fine (however labor intensive it may turn out to be).
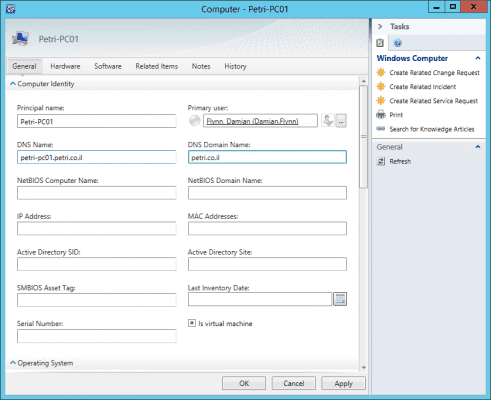
As an example, we will leverage the Service Manager console to manually create a “computer” configuration item without using the connector framework or by importing any information.
- Launch the Service Manager Console.
- Select the Configuration Items view.
- Expand the navigation tree, to select Configuration Items \ Computers \ All Windows Computers .
- From the Task Pane click Create Computer.
- The computer form will be presented, in which you can provide details related to this new item.
The fields offered on the form are sourced from the “computer” class in Service Manager. If you extended this class you can add or change fields to suit other devices (for example, phones). Of course, you would also want to create a custom view or form to see these extended fields.
- Now, you can fill out the form with the respective data for your computer. Some fields will have been marked as mandatory, so those will need to be addressed also.
- Click OK to create your new configuration item.
- At this point, SCSM will add the item to the database and assign a new unique GUID for the CI, which will be used with any relationship we will make to the item.
As you will appreciate, the procedure for creation is quite simple yet not very efficient. As an alternative to using the inbuilt connectors for the purpose of establishing all your configuration items, we can also leverage the integration packs in Orchestrator or the PowerShell modules, both of which permit for a managed approach to establishing your configuration database.
However, in the long run, the connector framework will ultimately prove to be the best approach, as any changes in environment will be automatically synchronized into the CMDB, without any need for daily interaction ensuring the CMDB is always up to date.