Command Line Event Logs – Part 1
Overview
Don’t get me wrong, graphical tools are just fine. However, I tend to spend a lot of time at the command line and can often type commands faster than I can navigate through a GUI. Plus, if I’m looking for ways to build an automated administrative task, command line tools are essential. You might think all I care about is Windows PowerShell. And while PowerShell is indeed an incredible tool, I realize some IT Pros aren’t ready for it or for one reason or another can’t use it. But all is not lost.
Let me show you a command line tool you have on your Windows 7 desktop that you can use to manage event logs. Actually, this tool has been around since Windows Vista, but since command line tools rarely get the love they deserve I’m expecting many of you have never seen this.
Managing Event Logs with the Command Line
Open a command prompt and look at help for WEVTUTIL.EXE
C:\> wevtutil /? Windows Events Command Line Utility. Enables you to retrieve information about event logs and publishers, install and uninstall event manifests, run queries, and export, archive, and clear logs. Usage: You can use either the short (for example, ep /uni) or long (for example, enum-publishers /unicode) version of the command and option names. Commands, options and option values are not case-sensitive. ...
There’s much more to the help than what I’ve shown here. But as you can see this is a pretty feature rich tool. In this part we’ll look at using it to query event logs.
The default behavior is that the command queries logs on the local computer. But we can use the /r parameter and specify a remote computer. Unfortunately, you can only query one computer at a time. But let’s not get ahead of ourselves. The basic way to use WEVTUTIL is like this:
C:\> wevtutil qe <logname> <command parameters>
Table 1 shows you the parameters you are most likely to use:
Table 1
| Parameter | Description | Example |
| /c:<count> | Return a specified count of event log entries. If omitted, you’ll get everything. | /c:5 |
| /rd:<True|False> | Reverse Direction. By default entries are returned oldest first. When set to True you’ll get newest entries first. | /rd:true |
| /f:<Text|XML|RenderedXML> | The default output format is XML. Set this to Text; easier to read output. | /f:text |
| /r:<computername> | Specify the name of a remote computer. | /r:server01 |
When connecting remotely, the utility will use your current credentials. But you can use /u:domain\username and /p:<password>
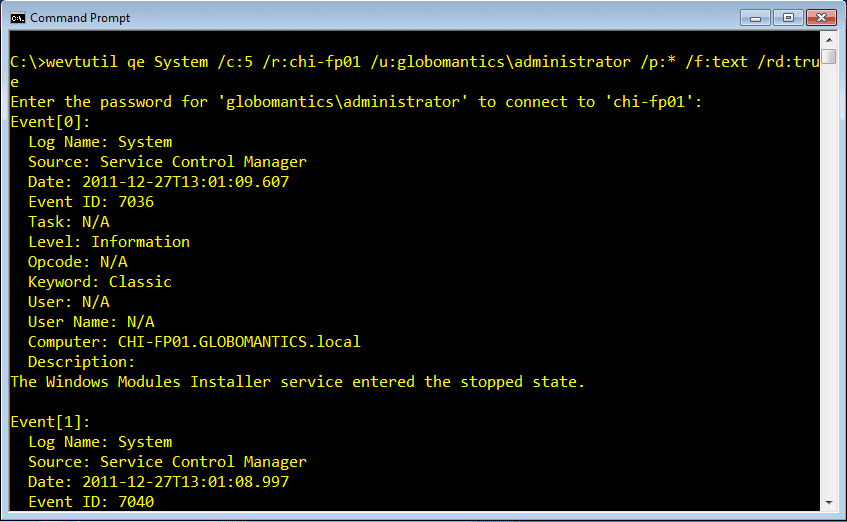
So to put this all together, let’s say I want to get the last 5 entries in the System event log on CHI-FP01.
C:\> wevtutil qe System /c:5 /r:chi-fp01 /u:globomantics\administrator /p:* /f:text /rd:true
I didn’t want to type the password in clear text, so I used an asterisk for the password which leads to a prompt, as you see in Figure 1.
Figure 1 Remote Query
I expect most of the time you will be searching for specific entries. This is where it gets tricky because Windows event logs now require a fair bit of XML knowledge. To find specific event log entries you need to use the /q parameter which requires a XPath query. Don’t worry if you don’t know XPath. For most IT Pros, I think you can use this template:
"/q:*[<logname>[(<xmlvalue=value>)]]"
The XML value is the name of the XML node. Grab an entry to see what one looks like.
C:\>wevtutil qe System /c:1
<Event xmlns='http://schemas.microsoft.com/win/2004/08/events/event'><System><Provider Name='Microsoft-Windows-Winlogon' Guid='{DBE9B383-7CF3-4331-91CC-A3CB16A3B538}'/><EventID>7001</EventID><Version>0</Version><Level>4</Level><Task>1101</Task><Opcode>0</Opcode><Keywords>0x2000000000000000</Keywords><TimeCreated SystemTime='2010-03-31T18:35:42.122671900Z'/><EventRecordID>13218</EventRecordID><Correlation ActivityID='{67144949-5132-4859-8036-A737B43825D8}'/><Execution ProcessID='440' ThreadID='456'/><Channel>System</Channel><Computer>CLIENT1.jdhlab.local</Computer><Security UserID='S-1-5-18'/></System><EventData><Data Name='TSId'>1</Data><Data Name='UserSid'>S-1-5-21-3957442467-353870018-3926547339-500</Data></EventData></Event>
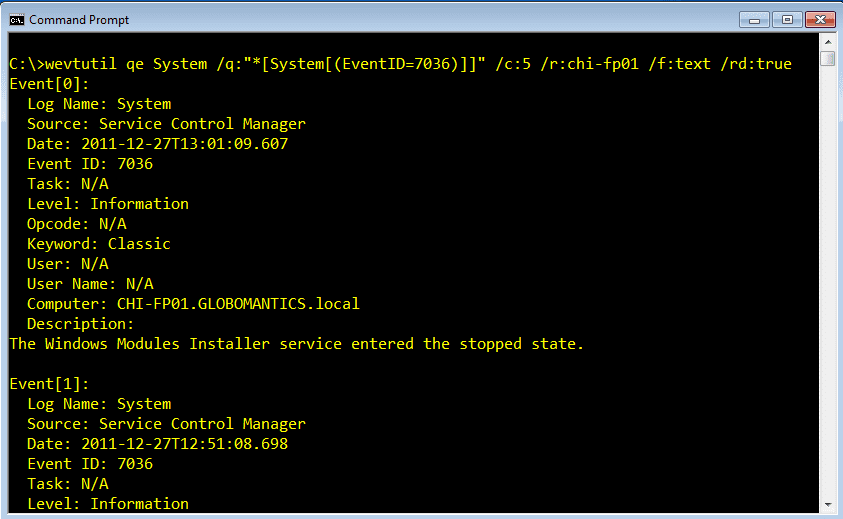
Now you see why I prefer to format as text. Let’s say we want to query on EventID 7036. I will run a command like this, using my current credentials.
C:\> wevtutil qe System /q:"*[System[(EventID=7036)]]" /c:5 /r:chi-fp01 /f:text /rd:true
You can see the results in Figure 2.
Figure 2 EventID Query
Another common task is to get entries by type, such as Error or Warning. You can still do this, but you’ll need to correlate them to a Level.
Table 2
| Level | Description |
| Level 1 | Critical |
| Level 2 | Error |
| Level 3 | Warning |
| Level 4 | Information |
Thus, to get the 5 most recent errors in the System event log from CHI-DC01, I would run this command:
C:\>wevtutil qe system "/q:*[System [(Level=2)]]" /f:text /c:5 /rd:True /r:chi-dc01 | more
I’m piping to MORE to page through the output. Or you can always send to a text file using console redirection.
C:\>wevtutil qe system "/q:*[System [(Level=2)]]" /f:text /c:5 /rd:True /r:chi-dc01 > d:\dc01-system-err.txt
You can even build a more complex query.
C:\>wevtutil qe system "/q:*[System [(Level=2 or Level=3)]]" /f:text /c:5 /rd:True /r:chi-dc01 | more
But be careful. Some of this is case sensitive and it isn’t always readily apparent where or why unless you are an XML expert. If you try the above using OR, it will fail as an invalid query.
Advanced Queries with Event Viewer Management Console
For more complex queries, the best thing to do is open the Event Viewer Management console and use the GUI to build your query. You can then look at the XML and copy and paste it into your command. Or if you have something you like to use often, save it to a text file and then “import” the query. For example, I built this XML query in the GUI:
<QueryList> <Query Id="0" Path="System"> <Select Path="System">*[System[Provider[@Name='Microsoft-Windows-EapHost' or @Name='Service Control Manager'] and (Level=1 or Level=2 or Level=3) and TimeCreated[timediff(@SystemTime) <= 604800000]]]</Select> </Query> </QueryList>
I copied and pasted it into a text file. Now I can use this query in a command line.
C:\>wevtutil qe s:\scmquery.txt /sq:true /c:5 /f:text /r:chi-fp01
Instead of a log name I specified the path to the XML query and set the /sq parameter to True. If there are no matching events, nothing will be returned.
That’s all the time I have for now. Next time we’ll look at using this utility to manage the event log itself.